Use case diagram for encryption and decryption Encryption process decryption storing passkey sharing without General steps encryption and decryption processes. encryption and decryption process diagram
Encryption and Decryption Process of 3DES. | Download Scientific Diagram
Encryption key types keys symmetric decryption diagram data cryptography figure same using ciphertext ico plaintext public figures Sequence diagram of the encryption and decryption process download images Block diagram of data encryption and decryption.
The flow chart diagram for the encryption and decryption process
Encryption tls decryptionFlowchart for encryption and decryption download scientific diagram Encryption and decryption process- end to endThe flow chart diagram for the encryption and decryption process.
Encryption and decryption process of 3des.Encryption decryption process Encryption symmetric works definition used example using when graphic aes shows securitySymmetric encryption 101: definition, how it works & when it’s used.

Basic block diagram of encryption and decryption process of proposed
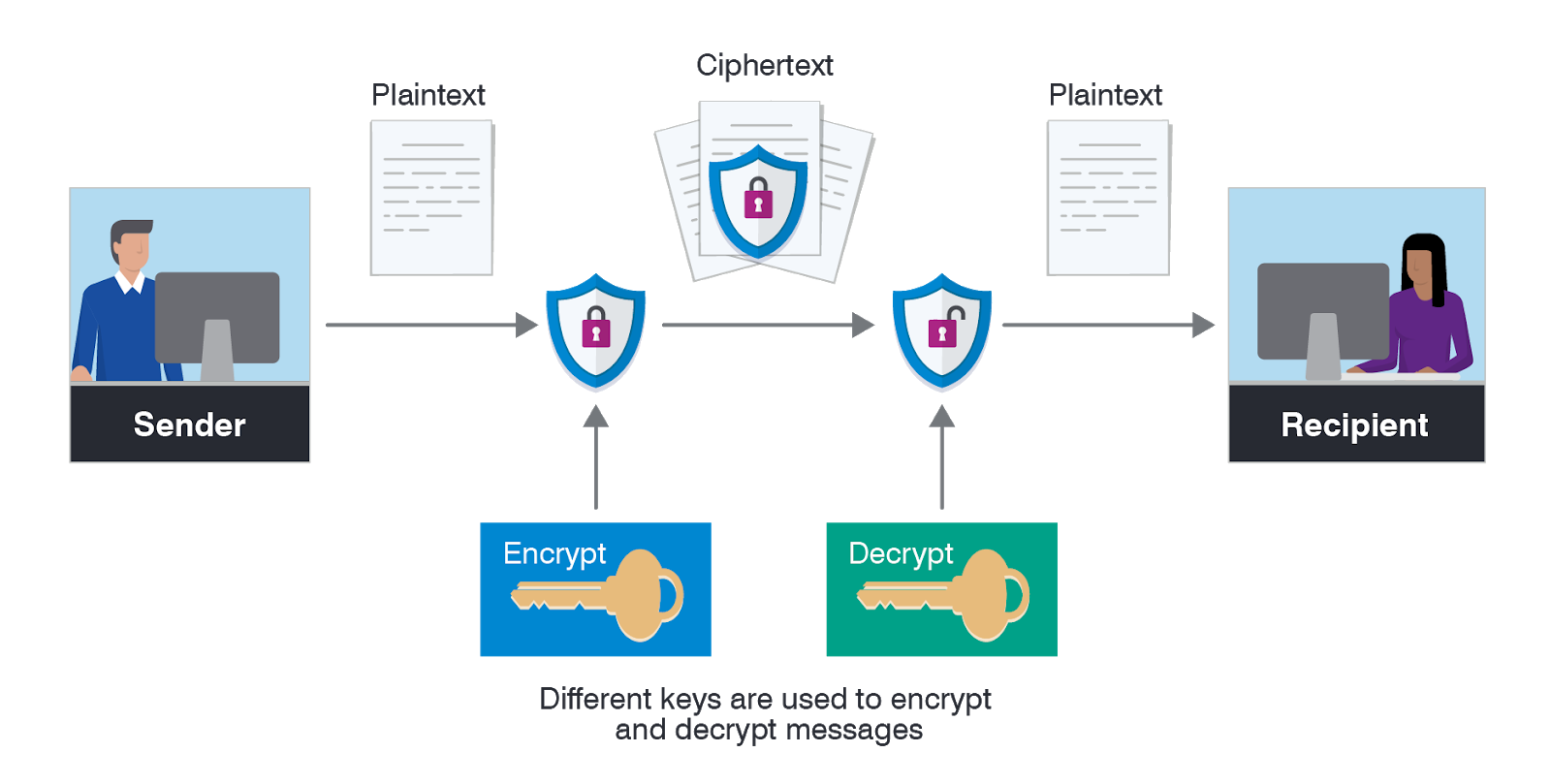
Encryption decryption encrypted encrypt decrypt hashing ciphertext salting zone frameworks aka wondering read accounts examinations thesslstoreEncryption decryption Encryption data types methods proofpoint definition numbers use place sender between receiver importance takes prime worksProcess of encryption and decryption [6]..
Encryption and decryption for sharing without storing a passkeyCentralized configuration for microservices using spring cloud config Encryption asymmetric does work data example works decryption use algorithms keys plaintext changesEncryption decryption schematic.

Types of cryptography
Encryption decryptionWhat is asymmetric encryption & how does it work? Schematic diagram of the encryption and decryption processes. the leftHow does https work?.
Data encryption-decryption processThe encryption and the decryption process in the encryption process 3des encryption decryption(a) schematic diagram of the encryption process. (b) schematic diagram.

Encryption and decryption process
Encryption decryptionEncryption and decryption process of aes. Flowchart of encryption process decryptionBlock diagram for encryption process.
Encryption and decryption process.Use case diagram for encryption and decryption Sequence diagram of the encryption and decryption processCryptography types diagram block source.

Mod 1 > week 1 > day 4
Encryption and decryption process.Types of encryption Encryption and decryption process using a key.Best and worst practices for tls/ssl.
End encryption decryption .



![Process of encryption and decryption [6]. | Download Scientific Diagram](https://i2.wp.com/www.researchgate.net/profile/Muhammad-Ehsan-Rana/publication/354888594/figure/download/fig1/AS:1086795429220352@1636123630648/Process-of-encryption-and-decryption-6.jpg)

